In 2023 we found a critical vulnerability in MySQL (CVE-2023-21980), allowing a rogue MySQL server to execute remote code on clients connecting to it.
In 2024 we discovered another issue in the mysqldump utility (CVE-2024-21096).
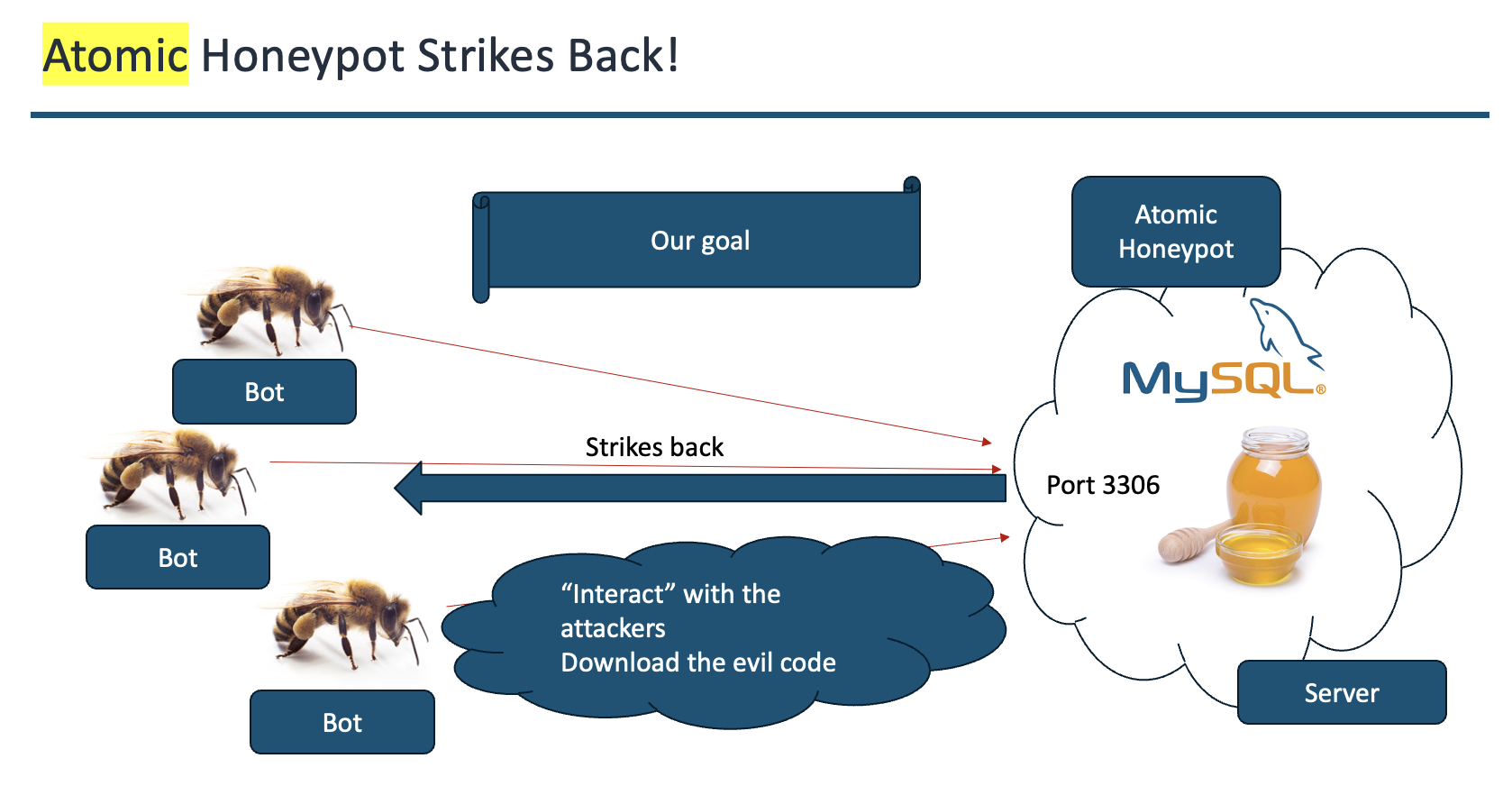
Leveraging these vulnerabilities, we developed an innovative honeypot designed not just to detect, but to counterattack malicious actors targeting MySQL systems.
At DEF CON 32, a live demonstration showcased how an attacker, intending to compromise a MySQL server, inadvertently triggered the honeypot's countermeasures, resulting in the execution of a reverse shell on the attacker's system.
This proactive approach not only defends against attacks but also gathers valuable intelligence on emerging threats.
Atomic Honeypot represents a paradigm shift in cybersecurity, transforming honeypots from passive monitoring tools to active defense mechanisms.
By leveraging known vulnerabilities, it not only protects MySQL servers but also provides critical insights into attacker methodologies, enhancing overall security posture.
For a comprehensive understanding and technical deep dive, watch the full presentation from DEF CON 32:
Atomic Honeypot: A MySQL Honeypot That Drops Shells - DEF CON 32 Presentation
Alexander Rubin
LinkedIn Profile